Small businesses should not overlook cybersecurity, as the risks are real and evolving. Partnering...
Everything You Need to Know Before a Cyber Attack
.png?width=1200&name=LinkedIn%20Blog%20Image%20(18).png)
It's not a matter of if, but when your organization will fall victim to cyber-crime.
Over the last decade, security specialists have warned companies and organizations to lock down their networks, enforce stringent policies, and reduce administrative access to slow down the momentum of the now billion-dollar cybercrime industry. At the same time, consumer products started flooding the home and workspace. USB drives were replaced with cloud apps and end-users admittedly forfeited permissions and privacy for convenience and high availability.
These two drastically different paths collided abruptly when Coronavirus (COVID-19) changed the global workplace. The need for employees to quickly connect from home to keep companies afloat meant that most organizations sacrificed the same thing: privacy and security. Without the proper oversight, licenses, and access controls, the robust corporate networks were reduced to the simplicity of a home Wi-Fi router.
How Can You Get Started With Secure Remote Access?
So, what do you do now that your business is either hybrid or fully "work from home" to obtain secure remote access and stay compliant? What if you are back in the workplace but many of your employees are still relying on consumer products? Let’s talk about a few steps to restore control while enhancing your organization’s cyber posture.
Start at the top, your company should understand the risk, regulations, and practices it will be held accountable for during the wake of a cyber-attack. If you do not already have a separate cyber security team available to discuss these matters, you need to get in front of the decision makers to place the following topics under Crisis or Disaster Management.
Here are some icebreakers to start the conversation: What is your chance of a flood, fire, cyber-attack? I would venture to believe that the cyber-attack, even at a low number like 10%, is a higher risk factor to your organization and therefore needs to be addressed in the same manner: time, resources, and money.
If you have not already, you must purchase cyber liability insurance. Start with that step!
Once you have cyber liability insurance, do you know what you are protecting? It may sound simple, but is it?
Every company should do an audit of their digital inventory tracked by constituent type or PII (Personally Identifiable Information). You need to know what is being stored, where it is stored, and what is the retention policy. The Data Inventory needs to track sensitive information down to the file level. It could be an app in the cloud, an excel file on a local server or workstation, even data stored in a phone app.
Make sure your employees have identified any place they keep sensitive information to ensure those pesky consumer products are not creeping into your organization. For example, if you find out someone is using a personal DropBox or iCloud, shut it down and make a policy against it.
Next Step? Identify Your Prized Data
Now that we know what exists it's time to identify what data is more important. Perform exercises with key members of the organization, asking the question can we survive without certain, specific data types? From there, and through other discussions, identify your prized data. This is what you must work to protect first. This is the cornerstone of your organization and therefore worth the most to cyber criminals. Once you have a repeatable practice, you can use these steps to secure all the data types in your organization.
Going back to the topic of cyber liability insurance, now that you have identified your prized data, you can place a value on it. IBM places *$180 US per record for PII lost in a breach. Now that you have the numbers to do the math, did you buy enough cyber liability insurance? What level of RISK is your company willing to take?
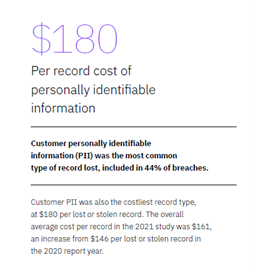
*Key Findings from the IBM Security Cost of a Data Breach Report 2021
What About Compliance?
You have probably already heard of compliance regulations such as HIPPA, COPPA, or PIPPA. But do you have organizational policies around them? Better yet, have employees been trained to clearly know enough about these regulations to handle the data responsibly?
When GDPR (EU General Data Protection Regulation) hit in 2018 most US companies had to scramble to ensure the needs of their oversea customers were met. Since that time, many different data regulations have hit the state or congress floor.
Make sure you have someone inside your organization whose job it is to stay aware of these regulatory bodies not only for your state headquarters, but for the state in which your customers reside. If you don't have a knowledgeable IT professional working within your organization, then learn more about how managed compliance as part of your overall IT security strategy can help.
Again, it is not a matter of if but when regulations around data protection will hit you. So why not start early to avoid a late scramble or an embarrassing lawsuit?
.png?width=1200&name=LinkedIn%20Blog%20Image%20(19).png)
What should you do with those end-users?
This is where security frameworks like NIST, CPL, and others come in to play. NIST is arguably the most complete and generic. Meaning you can apply those practices to any size business and to many industries. Remember that Data Inventory from earlier? Now we need to know who has access to it.
How you handle giving access to employees throughout the organization can be addressed in your Access Control Policy. This is one of the main things you need to track and maintain when building out your cyber security plan. Knowing who has access to that prized data is the only way you can truly secure it. By removing rights that are not necessary, for this and other applications, you are also reducing your organization’s overall risk. If they don’t have access to it, they can’t misuse it, and neither can the cyber criminal who gains access to their account.
Here are some other important cyber safety policies:
- Account Management Policy (How they are created, onboarding and offboarding)
- Information storage and retention policies (Encryption rules and how long data is stored)
- Backup and Recovery Policy (Must be up to date to help against a ransomware attack)
- Asset Management Policy (Keep your employees using devices you can manage)
- Incident Response Policy (Who do they contact? What is done?)
- Security Training and Awareness Policy (Keep track of the training and promote accountability throughout the organization. We've partnered with KnowBe4 to offer a free training program)
- Remote Worker Policy (See below)
That last tip is a vital one! How are you mandating that your remote users handle data in a fashion that is secure when they are not in the office or under your corporate umbrella?
This policy should also contain sections for vendors, contractors, managed service providers, consultants, and anyone who accesses your organizations environment.
Once you agree on a remote policy (for example: only store information on a shared corporate drive via a VPN), companies like Data Networks can lead you to the most secure and cost-effective solution. But to truly make your organization more secure their needs to be a commitment to only use approved devices, applications, and transport mechanisms (like encrypted email) when handling sensitive information. This is where the human firewall comes into play. All users share this responsibility, and all users are active participants in your security posture. How we make passwords, what access we give, and how we classify data are all part of preventing cyber attacks.
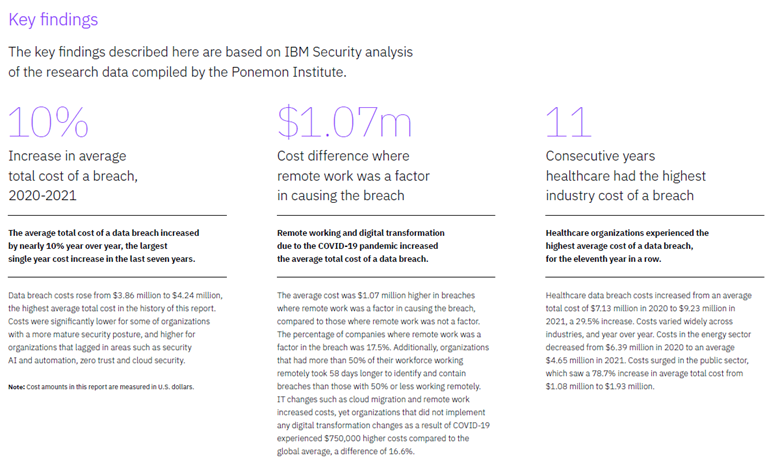
*Key Findings from the IBM Security Cost of a Data Breach Report 2021
Take the next steps to protection your organization
This was just a taste of the complexity that comes with developing a cyber security program. It is a complex issue that takes a lot of work, but it is integral to protecting your organizations from cyber criminals. Our team at Data Networks have a dedicated and highly skilled staff who can help handle all your cyber security needs and continue the steps to optimal safety.
Don't forget to follow our blog for more tips on cybersecurity, compliance, and the newest IT trends!
.



.png?height=200&name=LinkedIn%20Blog%20Image%20(8).png)
.png?height=200&name=LinkedIn%20Blog%20Image%20(12).png)